Robust mesh watermarking
ACM SIGGRAPH 1999 Proceedings, 69-76.
Imperceptible low-frequency shape perturbations resilient to remeshing.
Abstract:
We describe a robust method for watermarking triangle meshes. Watermarking provides a mechanism for
copyright protection of digital media by embedding information identifying the owner in the data. The bulk
of the research on digital watermarks has focused on media such as images, video, audio, and text. Robust
watermarks must be able to survive a variety of "attacks", including resizing, cropping, and filtering.
For resilience to such attacks, recent watermarking schemes employ a "spread-spectrum" approach —
they transform the document to the frequency domain and perturb the coefficients of the perceptually most
significant basis functions. We extend this spread-spectrum approach to work for the robust watermarking
of arbitrary triangle meshes.
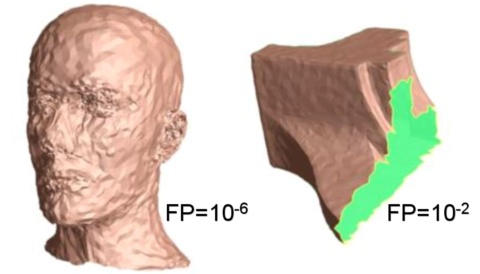
Generalizing spread spectrum techniques to surfaces presents two major challenges. First, arbitrary surfaces lack a natural parametrization for frequency-based decomposition. Our solution is to construct a set of scalar basis function over the mesh vertices using multiresolution analysis. The watermark perturbs vertices along the direction of the surface normal, weighted by the basis functions. The second challenge is that simplification and other attacks may modify the connectivity of the mesh. We use an optimization technique to resample an attacked mesh using the original mesh connectivity. Results show that our watermarks are resistant to common mesh operations such as translation, rotation, scaling, cropping, smoothing, simplification, and resampling, as well as malicious attacks such as the insertion of noise, modification of low-order bits, or even insertion of other watermarks.
Generalizing spread spectrum techniques to surfaces presents two major challenges. First, arbitrary surfaces lack a natural parametrization for frequency-based decomposition. Our solution is to construct a set of scalar basis function over the mesh vertices using multiresolution analysis. The watermark perturbs vertices along the direction of the surface normal, weighted by the basis functions. The second challenge is that simplification and other attacks may modify the connectivity of the mesh. We use an optimization technique to resample an attacked mesh using the original mesh connectivity. Results show that our watermarks are resistant to common mesh operations such as translation, rotation, scaling, cropping, smoothing, simplification, and resampling, as well as malicious attacks such as the insertion of noise, modification of low-order bits, or even insertion of other watermarks.
Hindsights:
It would be nice to run side-by-side comparisons with some other recent mesh watermarking schemes
such as Benedens 1999 or the
spectral approach of Ohbuchi et al 2001.
One major difficulty is judging the relative perceptibility of different watermarks.
See content copyrights.