Practice-Driven Cryptographic Theory
Cryptographic standards abound: TLS, SSH, IPSec, XML Encryption, PKCS, and so many more. In theory the cryptographic schemes used within these standards solve well understood problems, yet a parade of damaging attacks leave us with the question: What gives?
Theoreticians often suggest (at least in private) that the problems are well-understood and attacks arise because standardizers misunderstand cryptographic theory. I’ll use some of my recent work which uses provable-security techniques to analyze important standards (including TLS, HMAC, and PKCS#5) to argue that, just as often, it is the theoreticians who don’t have all the answers: analyzing practically-useful cryptography requires pushing models and proof techniques in never-before-considered directions. We’ll see how (what I’ll call) practice-driven cryptographic theory can lead to new understanding and improved confidence in cryptographic practice.
This talk will cover joint work with Mihir Bellare, Scott Coull, Yevgeniy Dodis, Kevin Dyer, Kenneth Paterson, Thomas Shrimpton, John Steinberger, and Stefano Tessaro.
Speaker Details
Thomas Ristenpart is an assistant professor in the Department of Computer Sciences at the University of Wisconsin – Madison. In Fall 2010, he completed his PhD in the Computer Science and Engineering department at the University of California at San Diego where he was a member of the Security and Cryptography Group. In September 2005, he received his Master’s degree from the University of California at Davis, where he was a part of the security group and the cryptography group. Thomas also received his Bachelor’s from UC Davis in June 2003. His research is in computer security, with recent topics including cloud computing security, applied and theoretical cryptography, and privacy.
- Series:
- Microsoft Research Talks
- Date:
- Speakers:
- Thomas Ristenpart
- Affiliation:
- University of Wisconsin - Madison
-
-
Jeff Running
-
Series: Microsoft Research Talks
-
-
-
-
Galea: The Bridge Between Mixed Reality and Neurotechnology
Speakers:- Eva Esteban,
- Conor Russomanno
-
Current and Future Application of BCIs
Speakers:- Christoph Guger
-
Challenges in Evolving a Successful Database Product (SQL Server) to a Cloud Service (SQL Azure)
Speakers:- Hanuma Kodavalla,
- Phil Bernstein
-
Improving text prediction accuracy using neurophysiology
Speakers:- Sophia Mehdizadeh
-
-
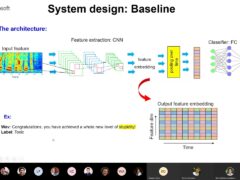
DIABLo: a Deep Individual-Agnostic Binaural Localizer
Speakers:- Shoken Kaneko
-
-
Recent Efforts Towards Efficient And Scalable Neural Waveform Coding
Speakers:- Kai Zhen
-
-
Audio-based Toxic Language Detection
Speakers:- Midia Yousefi
-
-
From SqueezeNet to SqueezeBERT: Developing Efficient Deep Neural Networks
Speakers:- Sujeeth Bharadwaj
-
Hope Speech and Help Speech: Surfacing Positivity Amidst Hate
Speakers:- Monojit Choudhury
-
-
-
-
-
'F' to 'A' on the N.Y. Regents Science Exams: An Overview of the Aristo Project
Speakers:- Peter Clark
-
Checkpointing the Un-checkpointable: the Split-Process Approach for MPI and Formal Verification
Speakers:- Gene Cooperman
-
Learning Structured Models for Safe Robot Control
Speakers:- Ashish Kapoor
-
-